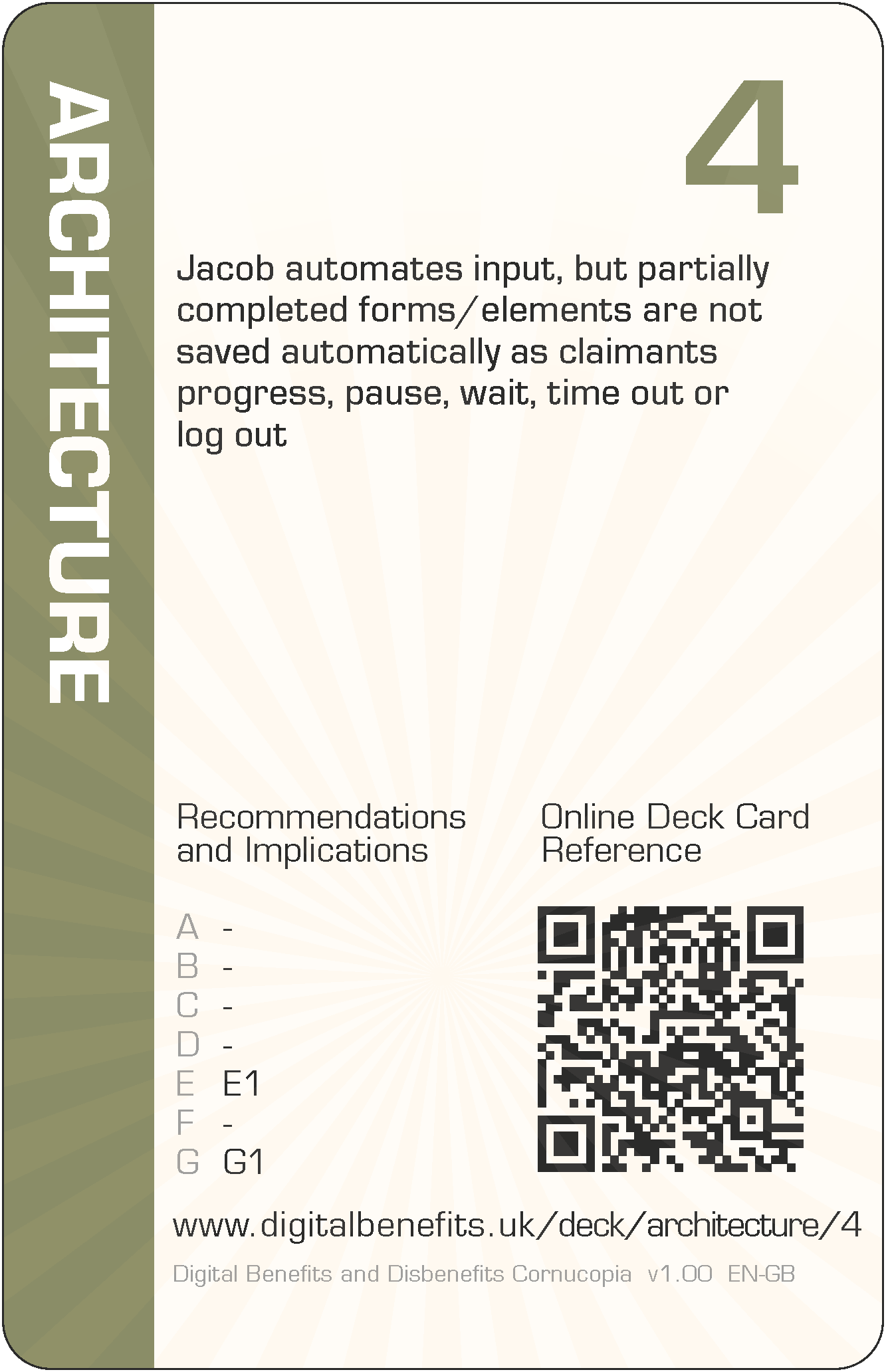
Architecture 4 (AR-4) Card
DBD Cornucopia > Deck > Architecture > 4
Card Details - Four of Architecture
Abbreviation
AR-4
Card's focus
The focus of this card is automatic saving
Threat to claimants
Jacob automates input, but partially completed forms/elements are not saved automatically as claimants progress, pause, wait, time out or log out
Threat to claimants
Jacob automates input, but partially completed forms/elements are not saved automatically as claimants progress, pause, wait, time out or log out.
Some examples of how this threat could lead to harms (negative effects on claimants)
The design recommendations and implications relevant to the card are listed below in the next section, but even those can be somewhat abstract and difficult to think about during practical day-to-day implementation. Therefore, some example harms are provided to complement the more formal research outputs. These examples are unique per card, and are only published on these web pages (i.e. in no other project outputs).
- Claimants lose information already entered online when they are distracted, or delayed, or pause to find information or to seek help, or have power, connectivity or device problems, or run out of money to access these
- Use of the browser back button in service websites means claimants lose information already entered, which they do not realise, or they do realise and have to re-key it
- Claimants expect forms to auto-save, and therefore lose information if they navigate to another part before manually saving
The examples are to help understand the threat on the card, not to suppress thinking and innovation. Incorporating these examples exactly, or closely matching ones, should be scored down when playing DBD Cornucopia as a game.
Applicable design recommendations and implications
These are reproduced here from Research Briefing N
Design systems which support the division of labour with claimants' ecosystems
- Integrate accurate specific and contextual primary guidance about making claims within systems and promote secondary professional assistance
None
Signpost when additional assistance should be sought and recognise the time and effort needed to complete these activities
- Indicate to claimants when professional advice is crucial
Some activities undertaken to receive a social protection payment award require much more specialist knowledge and experience than most citizens have; such involvement can counter complexity to avoid becoming overwhelmed; increase visibility of when claimants should check whether advice can help by highlighting higher-risk parts of the process; avoid overly simplifying processes which can hide the underlying and necessary complexity of making and maintaining a claim and thus discourage seeking knowledge and experience in the wider ecosystem.
General Notes
Card values (i.e. '4' for this card) are for game play and are not correlated with the severity of harm. This is because threats cannot be ranked directly since they can affect individuals in different ways due to situations and circumstances, or affect fewer or more claimants, or the harms can arise in claimants' support networks and wider society.
The threat description uses a person's name as the "attacker" (i.e. 'Jacob' for this card), which can be thought of someone involved with implementation. They could have any role which influence digitisation. So they could be a database administrator, or a copy writer, or a quality assurance specialist, etc, or all of these. Everyone could have some influence on the claimant threat described. The names were randomly selected from those currently most popular as given names for boys and girls (UK Office for National Statistics).
The example harms provided are drawn from the research data (which explored not only parts of existing services but also the effects of possible changes to those), from the author's own knowledge of web application development and testing, the author's own experience of helping citizens to claim Universal Credit (UC) and Personal Independence Payment (PIP), and from suggestions submitted by other people (make a suggestion). The threats and example harms do not necessarily exist in the current UC or PIP deployments or in ecosystems around those services, but they might well do.
All the cards in this Architecture suit are: 2 3 4 5 6 7 8 9 10 J Q K A
The other suits in the deck are: Scope, Agency, Trust, Porosity and Cornucopia (plus Jokers).
