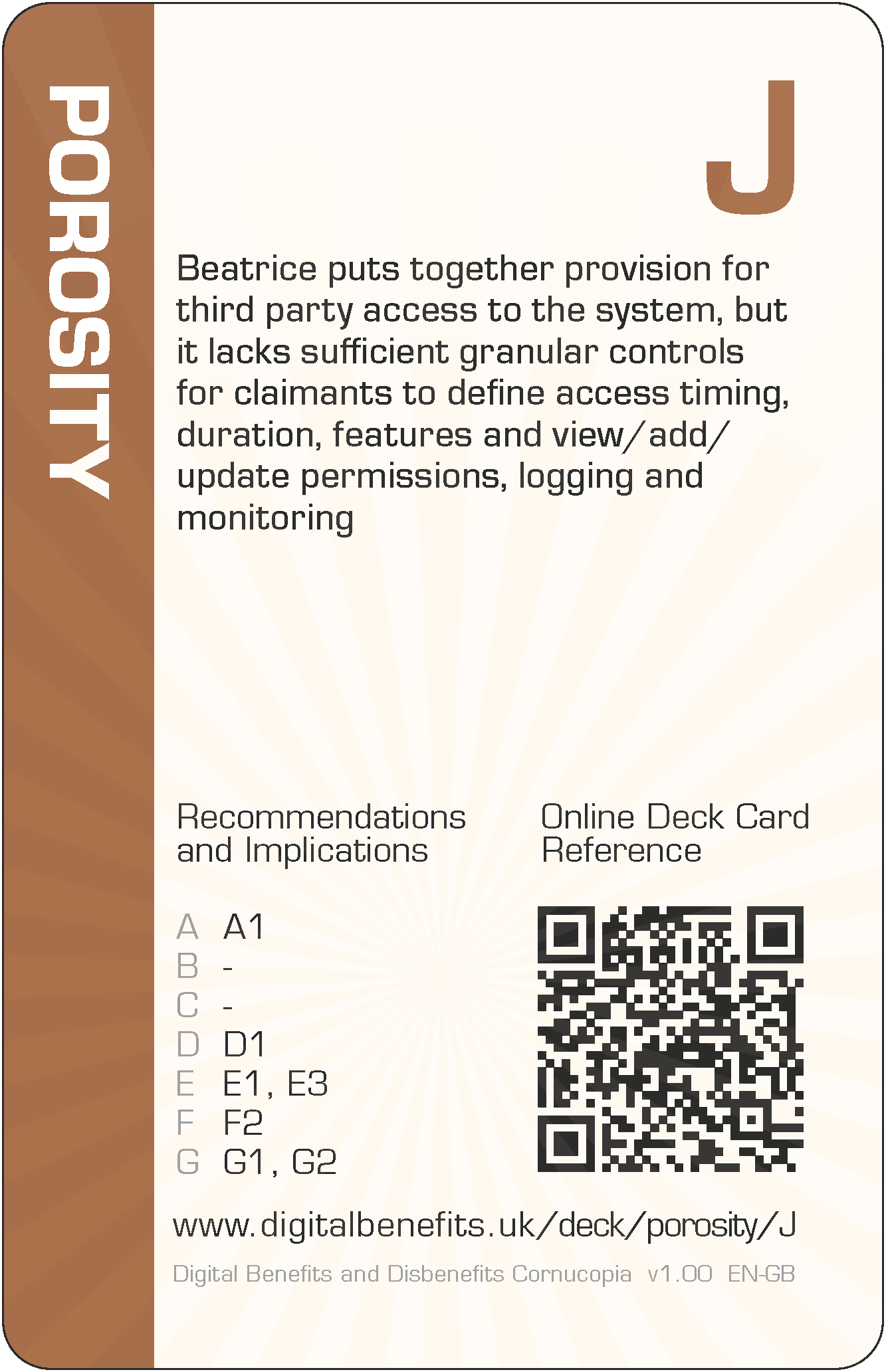
Porosity J (PO-J) Card
DBD Cornucopia > Deck > Porosity > J
Card Details - Jack of Porosity
Abbreviation
PO-J
Card's focus
The focus of this card is granularity of access control
Threat to claimants
Beatrice puts together provision for third party access to the system, but it lacks sufficient granular controls for claimants to define access timing, duration, features and view/add/update permissions, logging and monitoring
Threat to claimants
Beatrice puts together provision for third party access to the system, but it lacks sufficient granular controls for claimants to define access timing, duration, features and view/add/update permissions, logging and monitoring.
Some examples of how this threat could lead to harms (negative effects on claimants)
The design recommendations and implications relevant to the card are listed below in the next section, but even those can be somewhat abstract and difficult to think about during practical day-to-day implementation. Therefore, some example harms are provided to complement the more formal research outputs. These examples are unique per card, and are only published on these web pages (i.e. in no other project outputs).
- Claimants have to give all or nothing service access to a third party, which they think is dangerous and are therefore reluctant to do
- Claimants become reliant on third party support, so the claimants cannot continue the maintenance of claims themselves at later date
The examples are to help understand the threat on the card, not to suppress thinking and innovation. Incorporating these examples exactly, or closely matching ones, should be scored down when playing DBD Cornucopia as a game.
Applicable design recommendations and implications
These are reproduced here from Research Briefing N
Support claimants’ own ecosystems
- Recognise how wider ecosystems contribute to social protection service delivery
For these systems, the 'service user' is rarely just one person and there should be provision for other actors in people's wider ecosystems. Facilitate and aid these existing assets by enabling, encouraging and promoting information sharing, additional user roles with different privileges, delegated access, real-time-integrations, and other ways to involve the assistance of others.
Embrace a wider ecosystem and fuller claimant activity viewpoint for digitised public services
- Legitimise extensibility and customisation of digital infrastructure
Deploy technology in ways that will permit, support and advocate integration with digital welfare by other actors. Provide timely, free and open access to system information, supporting content, and details of upcoming changes and updates to support these efforts.
Design systems which support the division of labour with claimants' ecosystems
- Integrate accurate specific and contextual primary guidance about making claims within systems and promote secondary professional assistance
None - Recognise changing trust effects in design of digital systems
Claimants have different opinions about the trustworthiness and motivations of the state, unfamiliar claimants and other actors, which affect their tolerance to accept harms, requiring flexibility in choosing assistance and recognition how this trust can change over time: prior to making a claim, while maintaining a claim, and after ceasing to be a claimant.
Design to assist claimants across the full span of their own activities
- Accept, permit and encourage direct sole-use, shared-use, assisted use, and indirect intermediated use and proxy use of systems
The nature of activities requires flexibility in how claimants and other actors in ecosystems interact with each other and with state systems, and these can change over time.
Signpost when additional assistance should be sought and recognise the time and effort needed to complete these activities
- Indicate to claimants when professional advice is crucial
Some activities undertaken to receive a social protection payment award require much more specialist knowledge and experience than most citizens have; such involvement can counter complexity to avoid becoming overwhelmed; increase visibility of when claimants should check whether advice can help by highlighting higher-risk parts of the process; avoid overly simplifying processes which can hide the underlying and necessary complexity of making and maintaining a claim and thus discourage seeking knowledge and experience in the wider ecosystem. - Reduce barriers for claimants to seek assistance and allow time for this to occur
Provide pointers to claimants where they can obtain independent professional help ensuring there is always a choice of communication channels and sources, whether by self-service or from elsewhere in ecosystems. Avoid deadlines which limit claimants' opportunities to access assistance, providing sufficiently long periods for activities to include these actions if required.
General Notes
Card values (i.e. 'Jack' for this card) are for game play and are not correlated with the severity of harm. This is because threats cannot be ranked directly since they can affect individuals in different ways due to situations and circumstances, or affect fewer or more claimants, or the harms can arise in claimants' support networks and wider society.
The threat description uses a person's name as the "attacker" (i.e. 'Beatrice' for this card), which can be thought of someone involved with implementation. They could have any role which influence digitisation. So they could be a database administrator, or a copy writer, or a quality assurance specialist, etc, or all of these. Everyone could have some influence on the claimant threat described. The names were randomly selected from those currently most popular as given names for boys and girls (UK Office for National Statistics).
The example harms provided are drawn from the research data (which explored not only parts of existing services but also the effects of possible changes to those), from the author's own knowledge of web application development and testing, the author's own experience of helping citizens to claim Universal Credit (UC) and Personal Independence Payment (PIP), and from suggestions submitted by other people (make a suggestion). The threats and example harms do not necessarily exist in the current UC or PIP deployments or in ecosystems around those services, but they might well do.
All the cards in this Porosity suit are: 2 3 4 5 6 7 8 9 10 J Q K A
The other suits in the deck are: Scope, Architecture, Agency, Trust and Cornucopia (plus Jokers).
