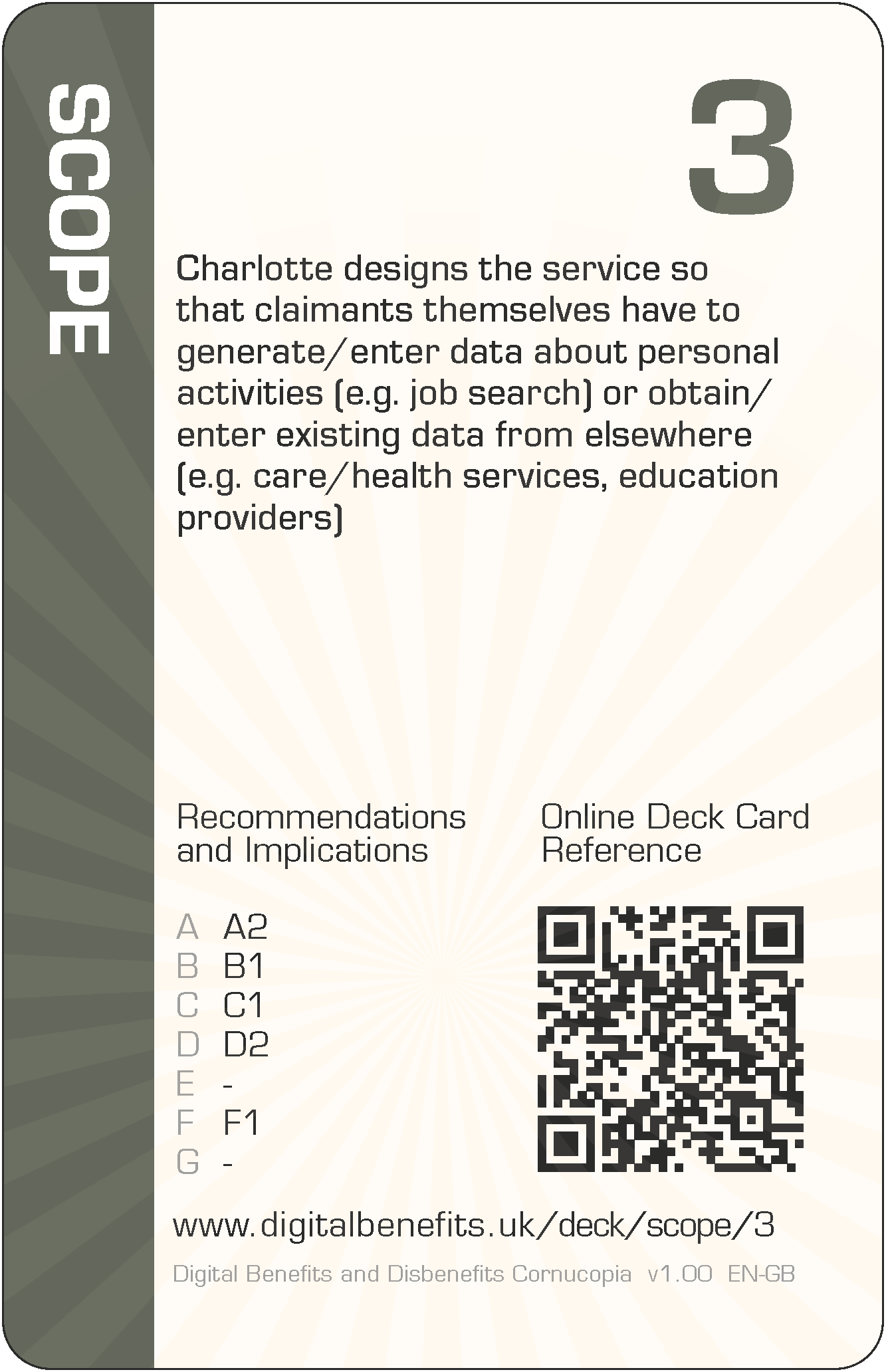
Scope 3 (SC-3) Card
DBD Cornucopia > Deck > Scope > 3
Card Details - Three of Scope
Abbreviation
SC-3
Card's focus
The focus of this card is data acquisition
Threat to claimants
Charlotte designs the service so that claimants themselves have to generate/enter data about personal activities (e.g. job search) or obtain/enter existing data from elsewhere (e.g. care/health services, education providers)
Threat to claimants
Charlotte designs the service so that claimants themselves have to generate/enter data about personal activities (e.g. job search) or obtain/enter existing data from elsewhere (e.g. care/health services, education providers).
Some examples of how this threat could lead to harms (negative effects on claimants)
The design recommendations and implications relevant to the card are listed below in the next section, but even those can be somewhat abstract and difficult to think about during practical day-to-day implementation. Therefore, some example harms are provided to complement the more formal research outputs. These examples are unique per card, and are only published on these web pages (i.e. in no other project outputs).
- Claimants have to book GP appointments to request health evidence (e.g. periodically a fitnote periodically, one-off medical history) themselves, taking their own time and effort, and also consuming extra resources at the GP practice
- Claimants have to do data collection clerical work themselves, instead of their being something implemented digitally to help collect existing information directly (e.g. from employers, health professionals, education authorities, landlords), and/or to help log/generate new data as it arises (e.g. employment search records, training activity logs
- Legacy paperwork has not been imported or has been disposed of or otherwise made inaccessible, so claimants are disadvantaged by having no access to the legacy records to prove their eligibility or to support their claims
The examples are to help understand the threat on the card, not to suppress thinking and innovation. Incorporating these examples exactly, or closely matching ones, should be scored down when playing DBD Cornucopia as a game.
Applicable design recommendations and implications
These are reproduced here from Research Briefing N
Support claimants’ own ecosystems
- Generate structured data for visibility and re-use by claimants and other actors
Provide, signpost and explain functionalities to span the fullest range of claimant activities, so as to reduce the need for and use of messaging/chat interactions (like the UC Journal) which result in unstructured data. Ensure the structured data enables re-use to increase wider ecosystem efficiencies: provide for recording and keeping full records of every interaction by every channel (including files, form submissions, all communications), and provide methods to ensure information can be found and referred to, and easily exported or shared with others as required.
Acknowledge claimants as people in digital design
- Prioritise claimants' interests over system efficiencies
All digital welfare design processes, methods and decision-making should prioritise claimants' needs to achieve best outcomes for individuals rather than system efficiencies. Organisational knowledge and resources should be utilised to this respect including intervening in advance to identify matters that affect claims or what claimants may have forgotten about.
Reduce claimants’ interaction burdens with digital welfare
- Shift the burden of gathering evidence from claimants towards the state
Transfer effort from claimants to the state, to improve timeliness and reliability. Prioritise the implementation of dig- ital processes to gather or import, check and use necessary data from internal and external providers. Change claimants' role to verifying the data, rather than providing it, and ensure claimants have visibility and control over derived status attributes.
Embrace a wider ecosystem and fuller claimant activity viewpoint for digitised public services
- Design for the needs of claimants’ lives covering their expansive activities
Recognise that service take-up requires more than direct interactions with the state. Ensure design is not restricted to service delivery between interaction points of claimants and the state within a 'user journey', and instead span all actors and mediating instruments that come together to achieve the claimant's goal.
Design to assist claimants across the full span of their own activities
- Provide capabilities for activities prior to, during and after direct public service interaction
Consider the temporal aspects of claimants' activities across the whole lifecycle from before making a claim to after ending an award. Acknowledge how earlier and repeated interventions can reduce later harms, empower claimants and increase the capabilities of claimants.
General Notes
Card values (i.e. '3' for this card) are for game play and are not correlated with the severity of harm. This is because threats cannot be ranked directly since they can affect individuals in different ways due to situations and circumstances, or affect fewer or more claimants, or the harms can arise in claimants' support networks and wider society.
The threat description uses a person's name as the "attacker" (i.e. 'Charlotte' for this card), which can be thought of someone involved with implementation. They could have any role which influence digitisation. So they could be a database administrator, or a copy writer, or a quality assurance specialist, etc, or all of these. Everyone could have some influence on the claimant threat described. The names were randomly selected from those currently most popular as given names for boys and girls (UK Office for National Statistics).
The example harms provided are drawn from the research data (which explored not only parts of existing services but also the effects of possible changes to those), from the author's own knowledge of web application development and testing, the author's own experience of helping citizens to claim Universal Credit (UC) and Personal Independence Payment (PIP), and from suggestions submitted by other people (make a suggestion). The threats and example harms do not necessarily exist in the current UC or PIP deployments or in ecosystems around those services, but they might well do.
All the cards in this Scope suit are: 2 3 4 5 6 7 8 9 10 J Q K A
The other suits in the deck are: Architecture, Agency, Trust, Porosity and Cornucopia (plus Jokers).
